A Caterham Seven Blog
-
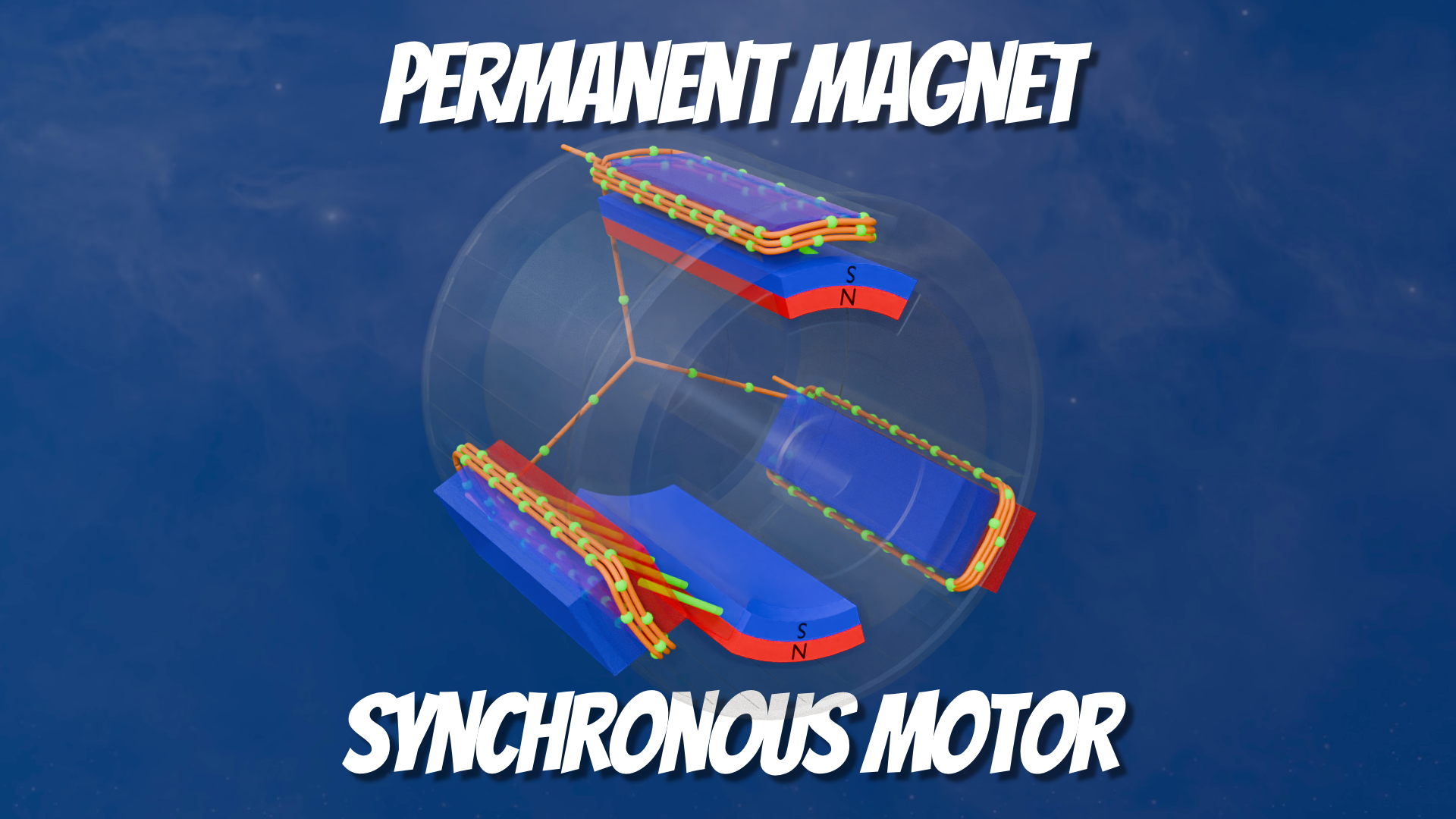
PMSM Motor Internals Video
As part of a larger explainer video I wanted to show how a Permanent Magnet Synchronous Motor Works. I wanted to show how the stator and rotor interacted with their respective magnetic fields and currents. The video shows how a simplified motor is constructed with a Stator and Rotor and then breaks those down to…
-

Finally a good Press-Stud Tool
This one’s as much a note for me so I know what I did to make this finally work. I’ve been looking for a decent way of fitting press-studs for things like boot covers. I’d tried the standard manual tap-and-hope tools that are supplied with the car and with SoftBitsForSevens kits. But that always seemed…
-

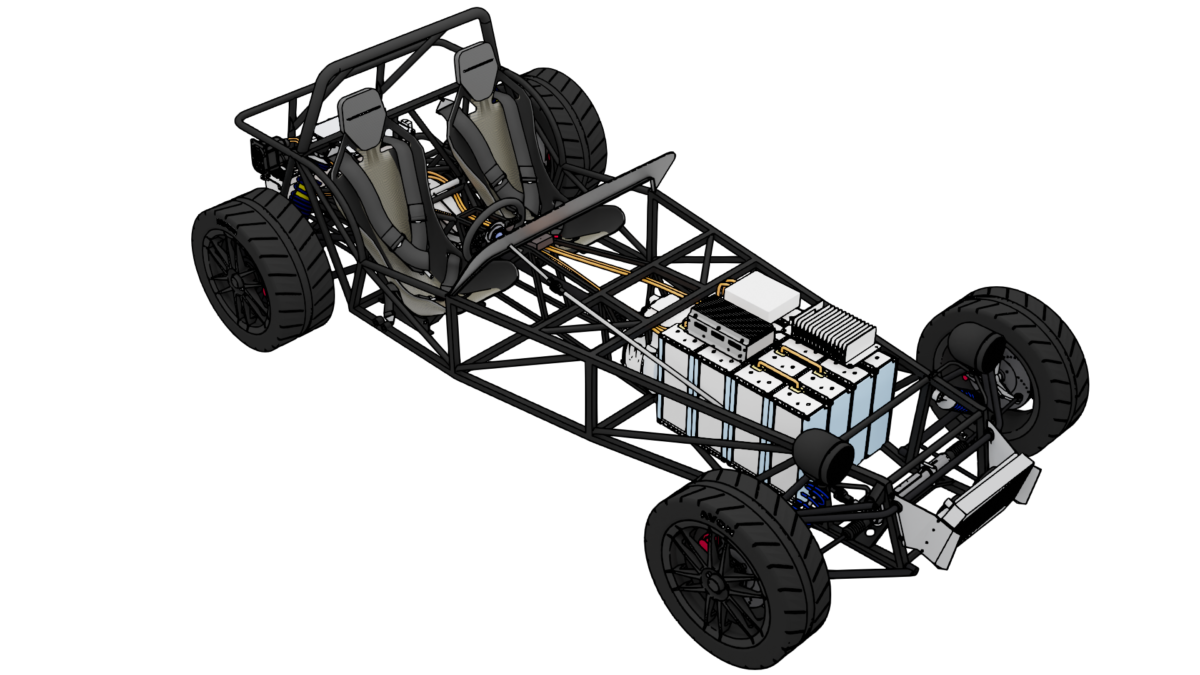
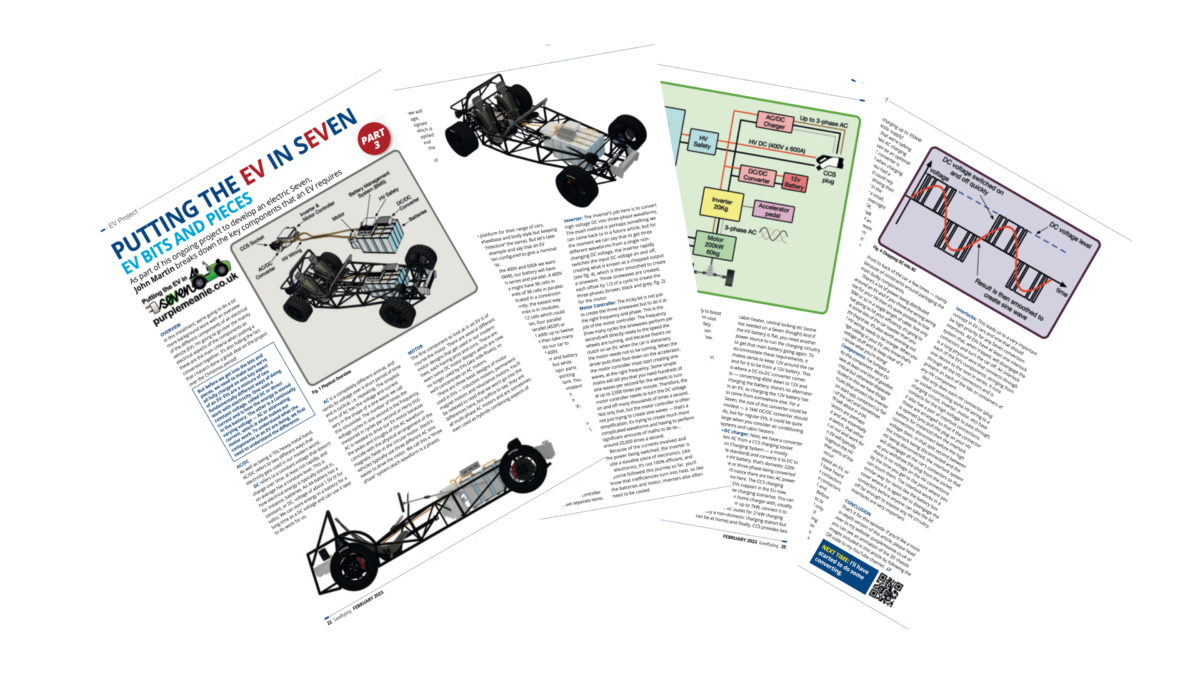
Putting the EV in sEVen – Youtube Project Kick-off
While I’ve been writing articles for the Caterham and Lost Seven Club’s Lowflying magazine, and doing a few Instagram and Facebook posts, I’ve not got around to creating the kick-off video for the Electric Seven Conversion project for Youtube, until now. I’m not really expecting this video to set the world alight, but it’s necessary…
Got any book recommendations?